Building next-generation software security requires architecting defenses that anticipate threats still evolving—from adversaries weaponizing AI to exploitation timelines collapsing from months to days. The threat landscape in 2026 is fundamentally different from five years ago. Attackers now integrate artificial intelligence into their intrusion tradecraft, social engineering campaigns, and information operations, while the volume of exploitable vulnerabilities has reached historic highs. For startups, the challenge is acute: you lack the security budgets of enterprise competitors, yet you often operate with older codebases, fewer security personnel, and legacy dependencies that create attack surfaces you don’t fully understand. Next-generation security isn’t about deploying more tools. It’s about rethinking the architecture of how software is built, deployed, and monitored—with the assumption that breaches will happen, and that your response time, not prevention alone, determines survival.
Companies that have successfully implemented modern security frameworks share three characteristics: they treat identity and access control as a foundational layer (not a feature to bolt on later), they automate vulnerability detection and response before humans can introduce delays, and they measure their security posture in terms of mean time to respond (MTTR) rather than mean time between failures. For a startup building a SaaS platform, this might mean moving from quarterly security audits to continuous vulnerability scanning, from storing database credentials in configuration files to implementing secrets management, and from hoping developers follow security guidelines to embedding threat modeling into your development process. The cost of getting this wrong is no longer theoretical. The global average data breach now costs $4.88 million, and most organizations take 277 days to identify and contain an incident—time enough for adversaries to steal intellectual property, customer data, and credentials. Cybercrime is projected to cost the world $23 trillion by 2027, a 175% increase from 2022. For a growing startup, a single breach can be existential, not just financially but in terms of customer trust and regulatory compliance.
Table of Contents
- What Makes Today’s Software Security Threats Different?
- The Vulnerability Explosion and Its Hidden Costs
- The Quantum Computing and Encryption Time Bomb
- Identity Security and Zero Trust as Foundational Layers
- The Risk of Partial Security Implementation
- Timeline Pressure and the Cost of Delay
- Building Security Culture as a Competitive Advantage
- Conclusion
What Makes Today’s Software Security Threats Different?
The volume and velocity of threats have fundamentally changed the security equation. In 2025 alone, 48,174 new CVEs were published—one of the highest annual totals recorded—and that pace has accelerated into 2026, with 131 new CVEs disclosed every day. The median time from vulnerability disclosure to active exploitation has collapsed to under five days, and over 54% of critical vulnerabilities face active exploitation within the first week of disclosure. For startups using open-source libraries or third-party dependencies (which is most startups), this timeline is a compression problem: you may not even know a vulnerable package exists in your dependency tree before attackers are already exploiting it in the wild. What amplifies this urgency is that 56% of tracked vulnerabilities can be exploited without authentication, and there’s been a 44% year-over-year increase in exploitation of public-facing applications. This means your API, your web portal, your cloud-hosted database endpoint—anything touching the internet—is a target.
A startup running a customer support portal or a SaaS application with a public login page is in the same threat category as a financial institution. The attacker doesn’t care that you’re not handling nuclear codes; they care that you might have customer payment data, proprietary algorithms, or access credentials to enterprise systems your customers use. The second game-changer is that artificial intelligence has entered the attacker’s toolkit. In 2025, 13% of companies reported an AI-related security incident, and 97% of those companies acknowledged they lacked proper AI access controls. Adversaries are using AI across intrusion tradecraft, social engineering, and information operations—which means phishing campaigns are becoming harder to detect, attack automation is becoming more sophisticated, and agentic AI systems will lower the barrier to entry for attackers significantly by 2026. A motivated attacker no longer needs a PhD in exploit development; they can use an AI model to identify vulnerable code patterns, generate custom exploits, and orchestrate multi-stage attacks.
The Vulnerability Explosion and Its Hidden Costs
The sheer volume of vulnerabilities creates a false sense of security for some organizations: they assume patching is impractical, so they patch nothing, betting on obscurity. Others swing to the opposite extreme, treating every CVE as critical, burning out their teams with endless patching cycles that provide no measurable security improvement. The reality is more nuanced and more dangerous. Not all vulnerabilities are equal, but determining which ones matter requires threat modeling, asset inventory, and continuous monitoring—exactly the practices most startups skip because they’re seen as overhead rather than defense. Consider a concrete example: a startup building a healthcare SaaS platform discovers that a library they depend on has a critical remote code execution vulnerability. They have five days before active exploitation in the wild. Their options are constrained: patch immediately and risk breaking dependent features, isolate the vulnerable component behind additional access controls (slowing deployment), or accept the risk and hope their network segmentation holds. Each choice has costs.
Patching might require recompiling and regression testing, consuming a week of engineering time. Isolation might require rearchitecting their data pipeline, consuming two weeks. Accepting the risk requires that they’ve already implemented network monitoring, intrusion detection, and incident response playbooks—which most early-stage startups haven’t. The hidden cost is that vulnerability management at scale requires automation. Manual review of CVE feeds is no longer viable. A modern security program for a startup should include continuous software composition analysis (SCA) tools that scan your dependencies daily, automated patching workflows for non-breaking updates, and integration with your CI/CD pipeline so that vulnerable code never reaches production. But these tools have setup costs, training costs, and false-positive rates that create alert fatigue. The limitation many startups face is that they can’t afford a dedicated security engineer to tune these systems until they’ve grown large enough that the security debt is already crushing them.
The Quantum Computing and Encryption Time Bomb
One of the most overlooked threats in next-generation security is not new; it’s dormant. “Harvest now, decrypt later” attacks involve adversaries collecting encrypted data today with the full knowledge that quantum computing advances will make current encryption obsolete within the next 5 to 10 years, allowing them to retroactively decrypt stolen information. If your startup is handling data that needs to remain confidential for years—customer information, proprietary source code, strategic plans—you should assume adversaries are already harvesting it for future decryption. The U.S. government and critical infrastructure operators have already moved: post-quantum cryptography migration is mandated by government for critical infrastructure in 2026. For startups, this means you have a window to migrate before quantum-capable decryption becomes a realistic threat, but that window is narrowing.
The challenge is that migrating from RSA or ECDSA encryption to post-quantum algorithms isn’t a simple library update. It touches cryptographic key management, certificate infrastructure, backup and recovery systems, and vendor dependencies. A startup that waits until quantum computers are practical has already made their legacy systems a liability. The practical implication: if you’re building security into your platform today, you should architect your encryption layer with cryptographic agility—meaning you design it so that swapping one algorithm for another doesn’t require a complete system redesign. This might mean abstracting cryptographic operations behind a service layer, using industry-standard key management systems (like AWS KMS or HashiCorp Vault), and documenting your encryption inventory so that you can identify every place cryptography touches your system. The limitation is that most startups treat encryption as a check-box feature (“we use TLS”) rather than an architectural property, which means they’re unprepared for the migration burden when it becomes urgent.

Identity Security and Zero Trust as Foundational Layers
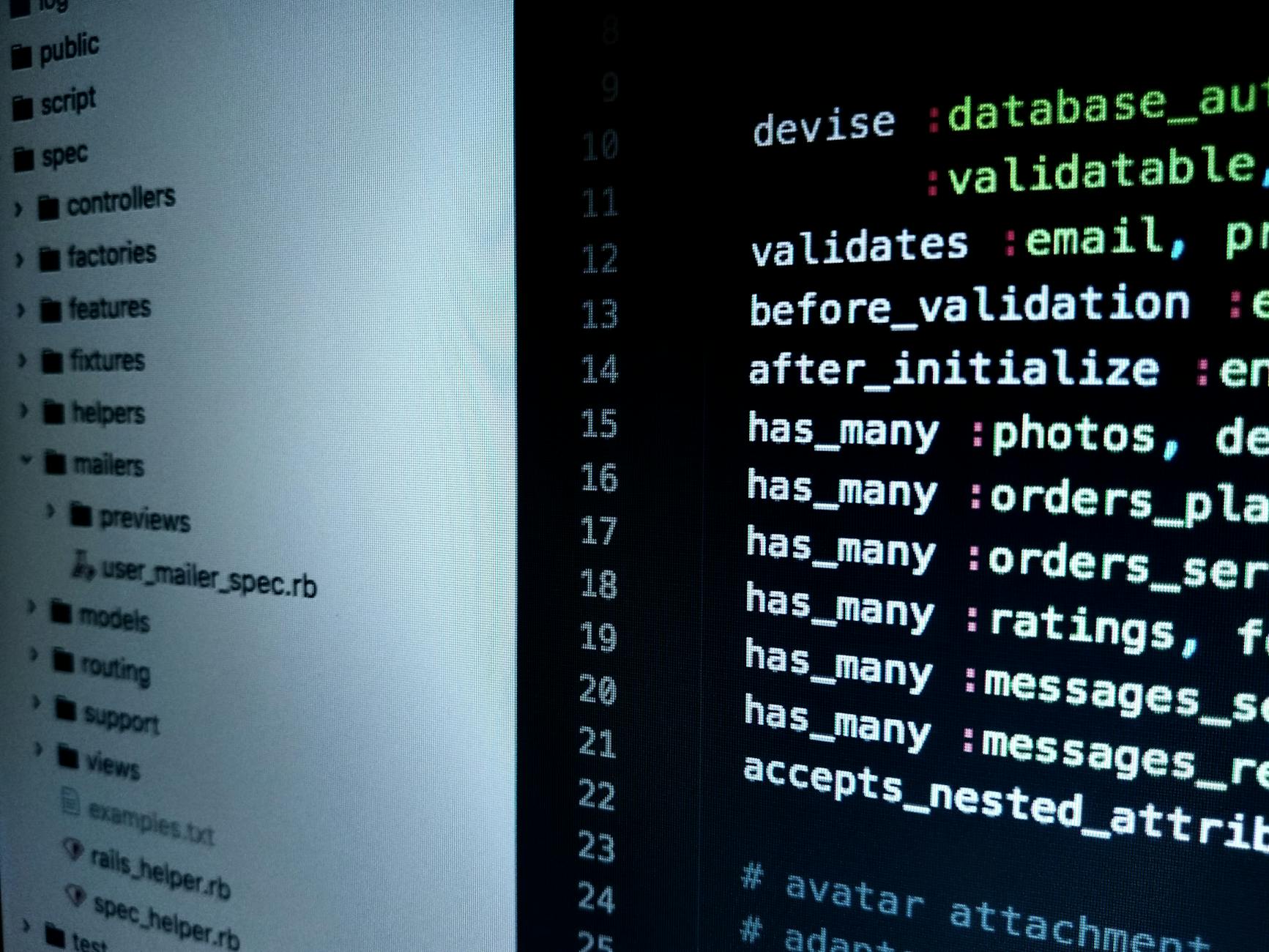
Industry consensus in 2026 points to identity security as the primary battleground in the AI economy. This is a shift in security priorities that many startups miss: they invest heavily in network firewalls and endpoint protection while leaving identity systems—the means by which users and applications prove who they are—as an afterthought. But if an attacker compromises an identity, they’ve already defeated your network defenses. They’re not attacking from outside anymore; they’re attacking from inside, using legitimate credentials. For a startup, this translates into specific, implementable practices. First: eliminate shared credentials and credentials stored in code or configuration files. Use identity services (like OAuth, SAML, or OIDC) that externalize authentication.
Second: implement zero trust architecture, which operates on the principle that trust is never assumed based on network location. Every request—whether from a developer’s laptop, a CI/CD pipeline, or a service in your cloud environment—requires authentication and authorization. Third: instrument your identity system with monitoring and alerting so that you can detect anomalous access patterns (a user accessing data at 3 AM from a new country, a service account making requests at ten times its normal rate) before they result in data loss. The tradeoff is complexity versus control. Implementing zero trust architecture is straightforward for startups building new systems from scratch; it’s exponentially harder for startups that already have legacy code paths and sprawling microservices. A monolith that trusts anything on the internal network can be retrofitted with zero trust, but the retrofit requires mapping every service dependency, implementing certificate-based mutual authentication (mTLS), and potentially rewriting entire subsystems. Many startups defer this work until after a security incident makes it non-negotiable, which is economically inefficient—the incident costs far more than the upfront investment would have.
The Risk of Partial Security Implementation
One of the most dangerous patterns in startup security is the illusion of coverage. A team implements intrusion detection but never reviews the alerts. They deploy a web application firewall but misconfigure the rules so that all traffic passes through unfiltered. They hire a security consultant who recommends a list of improvements, the team implements 30% of them, and then they claim to have “implemented security recommendations.” The problem is that security is systemic—a single weak link can compromise the entire architecture. This manifests in specific ways. A startup implements multi-factor authentication for employee accounts but leaves service accounts unprotected. They encrypt data in transit but not at rest.
They use strong passwords but store them in shared documents. They patch production systems but forget about development and staging environments where attackers often find credentials and API keys. Each of these gaps is individually manageable, but collectively they form an attack surface that adversaries will absolutely exploit. The warning here is that security is a comprehensive practice, not a checklist. A startup’s security posture should be measured against a framework—whether that’s the NIST Cybersecurity Framework, the CIS Critical Security Controls, or an industry-specific standard. Pick one, assess your current state against it, prioritize the gaps that create the most exploitable risk, and close them systematically. This requires that security decisions be made by teams with threat modeling expertise, not by committees of people guessing what matters. Many startups lack this expertise in-house, which is why security consulting, even for early-stage companies, is a worthwhile investment.
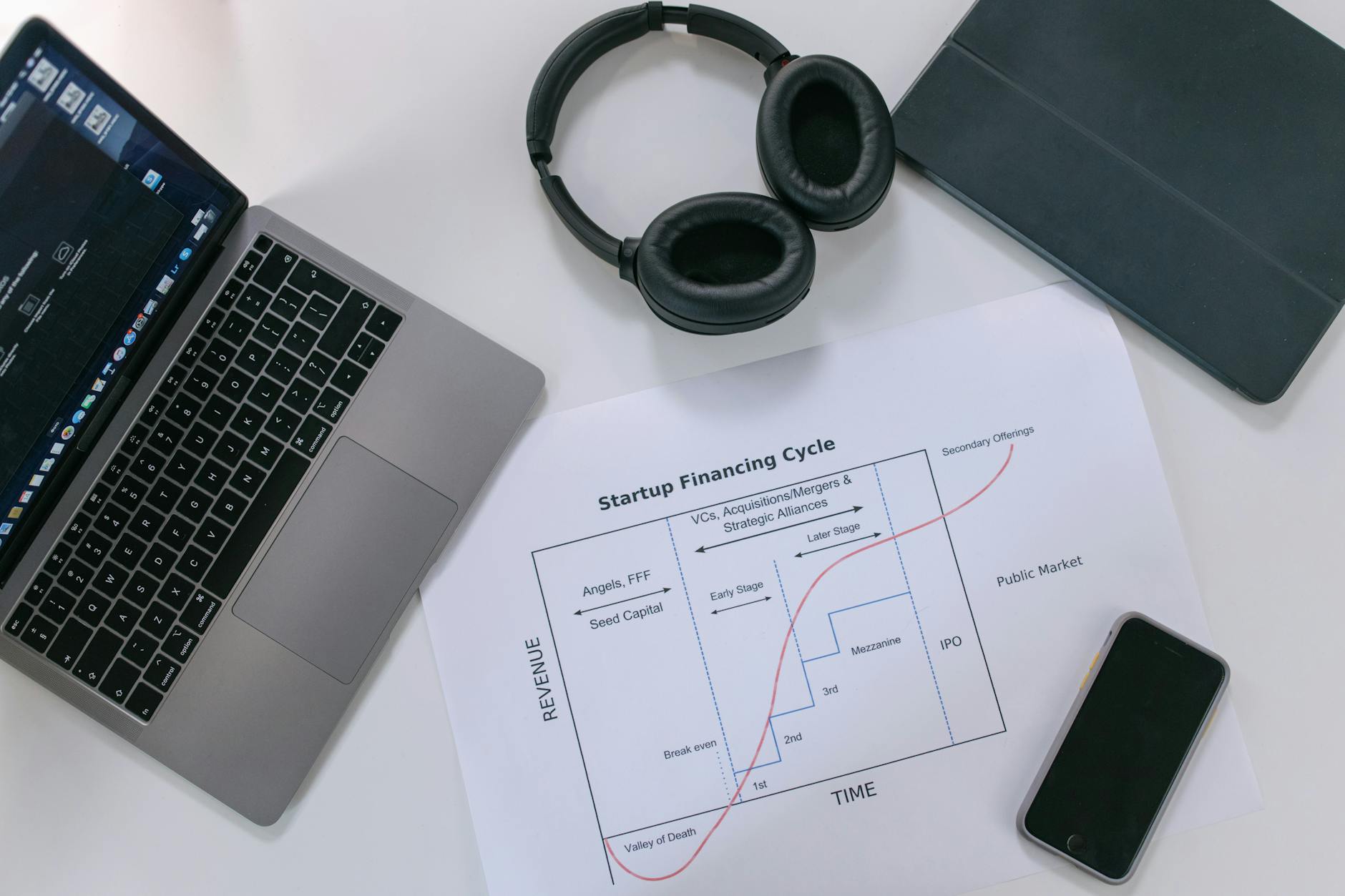
Timeline Pressure and the Cost of Delay
The 277-day average time to identify and contain a data breach isn’t just a statistic—it’s a business deadline. For most startups, a breach discovered after six months of attacker presence means credentials and data have already been sold on underground markets, customer trust is already damaged, and regulatory investigations are already underway. Compressing this timeline to weeks instead of months is a function of monitoring, alerting, and incident response playbooks that most startups don’t have. Consider the practical setup: A startup should implement centralized logging (collecting logs from every system and application into a searchable repository), real-time alerting (automated rules that flag suspicious activity), and tabletop exercises (simulated incidents where the team practices their response).
These aren’t exotic tools; they’re standard hygiene in modern security programs. But they require initial setup time and ongoing maintenance. A startup with five engineers might spend two weeks setting up centralized logging, and then an engineer needs to spend 30% of their time maintaining and tuning the system. That’s expensive. But it’s far cheaper than discovering a six-month-old breach and having to explain to your customers, regulators, and investors how the attacker remained undetected.
Building Security Culture as a Competitive Advantage
The most underrated aspect of next-generation security is culture. A startup with a security-first culture—where developers think about threat modeling during code review, where security considerations are discussed in sprint planning, where incidents are treated as learning opportunities rather than blame opportunities—will outcompete startups that treat security as a separate function. This isn’t because they’re technically superior; it’s because they’ve embedded security into their development process, which means vulnerabilities are caught earlier, response to incidents is faster, and the team’s threat awareness improves continuously. This requires leadership commitment.
A CEO who treats security as a cost center will build security as an afterthought. A CEO who treats security as a competitive advantage—something that builds customer trust and reduces operational risk—will hire security expertise, allocate resources to security infrastructure, and create accountability for security outcomes. For early-stage startups, this might mean hiring a fractional CISO or security architect early, even before you can justify a full-time security team. The investment in advice during the critical early-stage decisions (what cloud provider, what architecture, what dependencies) often prevents security debt that would otherwise require years to remediate.
Conclusion
Building next-generation software security for emerging technology threats is not about deploying cutting-edge tools or implementing every control that best practices recommend. It’s about making informed decisions about which threats matter to your business, architecting systems that can withstand current attack methods while remaining adaptable to future threats, and building a culture where security is everyone’s responsibility, not just the security team’s. The facts are sobering: 131 new vulnerabilities are disclosed daily, breaches take months to detect, and the cost of failure has reached multimillion-dollar scales. But the path forward is clear: start with identity and access control, implement continuous vulnerability monitoring, adopt zero trust principles, and measure your security posture against recognized frameworks.
For startups, the competitive advantage belongs to teams that make security decisions early and systematically. You can’t out-engineer the largest companies, but you can out-think them by making smarter architectural choices when the system is still small. The cost is upfront investment in planning, tooling, and expertise. The benefit is that you never face a breach that could have been prevented, and your growth isn’t constrained by security debt that forces expensive rearchitecting. Start now, measure progress quarterly, and treat security as a foundational layer of your business, not as a feature to add later.