Companies are preparing for quantum computing threats through comprehensive post-quantum cryptography migration, driven by urgent government mandates and the accelerating timeline for cryptographically relevant quantum computers. The NSA has given organizations until January 2027 to implement quantum-safe systems for national security purposes, while simultaneously, 2026 has been declared the “Year of Quantum Security” by an industry coalition led by the FBI, NIST, and CISA. These aren’t theoretical precautions—organizations like Google, Apple, and Cloudflare have already embedded post-quantum encryption into their infrastructure, recognizing that the window for preparation is closing rapidly.
The immediacy of this shift reflects a fundamental change in the threat landscape. Where quantum computers that could break modern encryption once seemed decades away, recent estimates suggest the computing power needed has shrunk dramatically: from requiring 20 million physical qubits in 2019 to potentially just 100,000 qubits by early 2026 under specific conditions. This accelerating timeline has forced companies to abandon the “wait and see” approach and instead commit to multi-year migration projects, restructure their cryptographic infrastructure, and prepare for what amounts to a wholesale rebuilding of how data security works across their operations.
Table of Contents
- Understanding the Quantum Computing Threat to Modern Encryption
- Government Mandates Are Forcing Corporate Action
- Post-Quantum Cryptography Standards Are Now Finalized
- Building a Migration Strategy Within the Time Constraint
- Market Dynamics Show the Scale of the Shift
- Real-World Implementation Examples
- The Timeline Ahead
- Conclusion
Understanding the Quantum Computing Threat to Modern Encryption
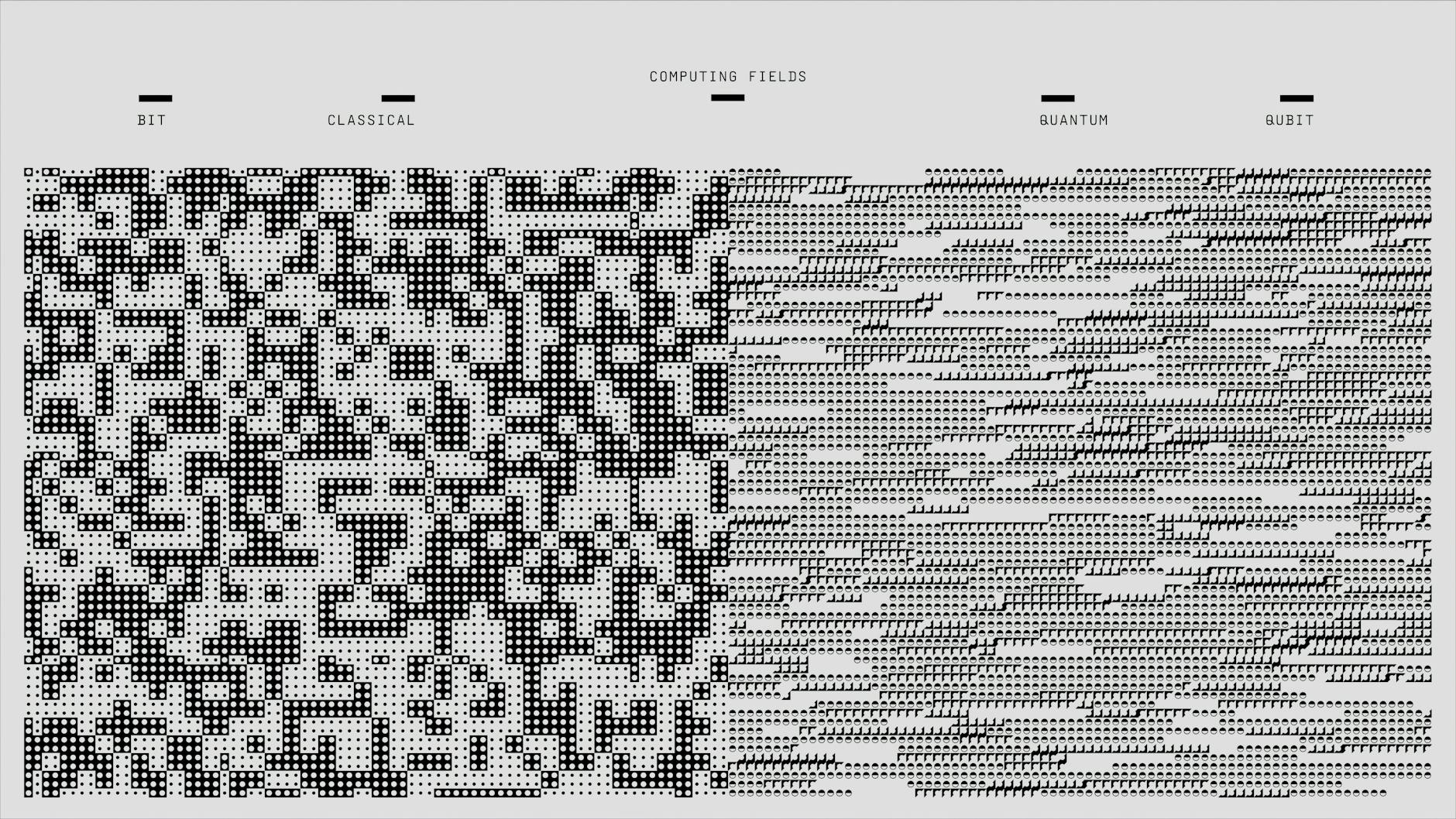
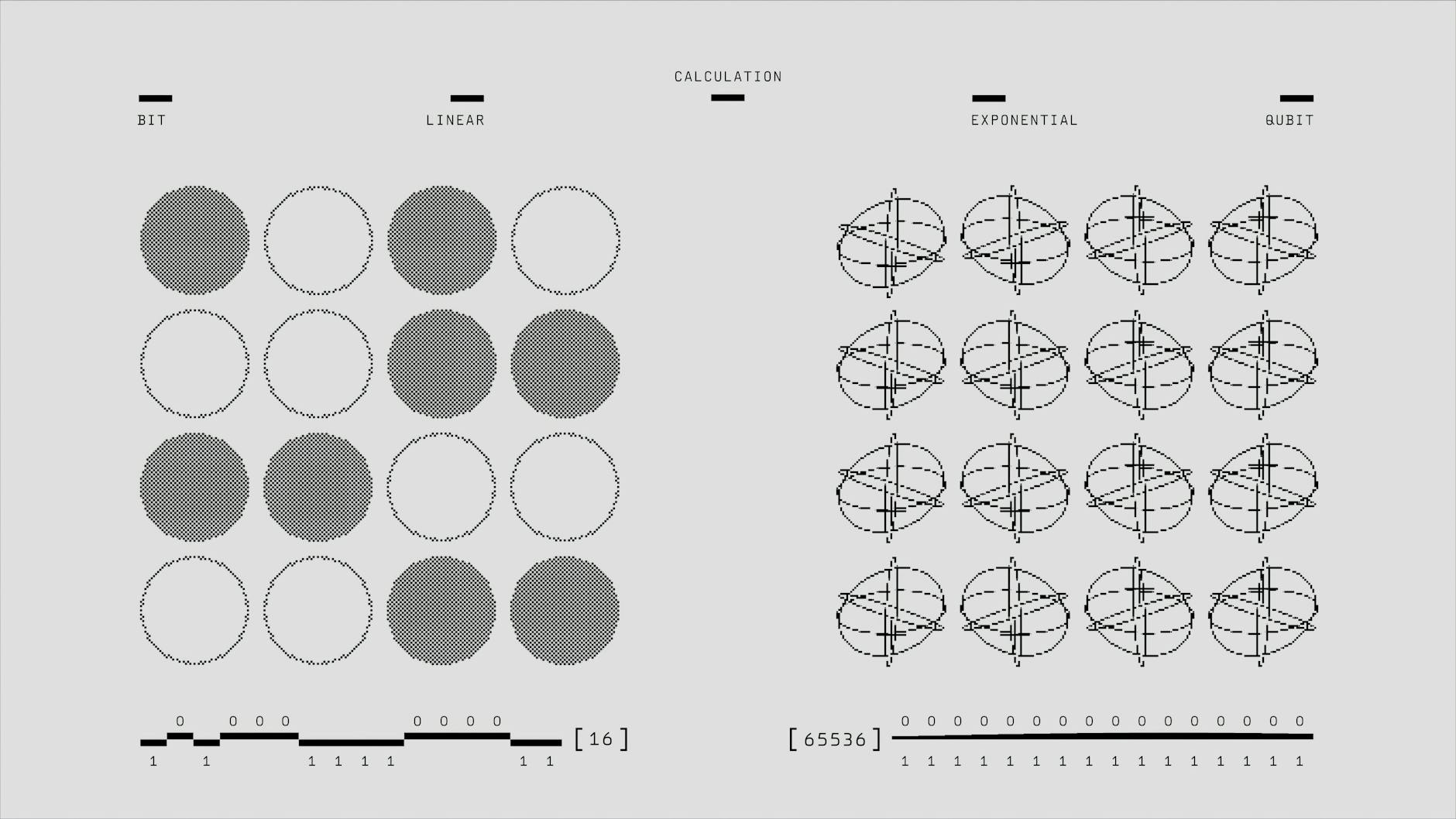
The quantum threat isn’t hypothetical—it’s a mathematical certainty that requires immediate action. Current encryption standards that protect everything from financial transactions to state secrets depend on the computational difficulty of breaking specific mathematical problems. Quantum computers, fundamentally different in how they process information, will render these problems trivial to solve. The challenge that currently takes classical computers billions of years might take a quantum computer minutes. What makes this especially dangerous is a strategy called “harvest now, decrypt later,” where adversaries collect and store encrypted data today with the intention of decrypting it once quantum computers become available.
Eighty-seven percent of organizations now rank this as a top security concern, yet many have only just begun taking action. The timeline for this threat is disturbingly compressed. While experts previously predicted a cryptographically relevant quantum computer (CRQC) could arrive around 2035, the qubit requirements for breaking current encryption have decreased dramatically in recent years. In 2019, breaking 2048-bit RSA encryption was thought to require 20 million physical qubits—an enormous number that seemed far away. Today, that estimate has fallen to under 1 million qubits, and some researchers propose it could happen with as few as 100,000 qubits under optimal conditions. This contraction of the timeline from theoretical to practically achievable has essentially shocked the security industry into action.
Government Mandates Are Forcing Corporate Action
The regulatory landscape has shifted dramatically in the past year, with government agencies transforming quantum security from an optional upgrade into a mandatory requirement. The NSA’s Commercial National Security Algorithm Suite 2.0 (CNSA 2.0) requires all new national security systems to be quantum-safe by January 2027—a deadline that applies not just to government agencies but to any contractor or vendor in the national security supply chain. For many companies, this means that contracts could be jeopardized if they don’t begin migration efforts immediately, since retrofitting systems typically takes 2 to 5 years.
Beyond individual regulatory requirements, 2026 has been declared the “Year of Quantum Security” by a coalition that includes FBI, NIST, and CISA leadership. This declaration signals a coordinated, government-wide push to accelerate quantum-safe adoption across both government and critical infrastructure. The declaration isn’t just symbolic—it’s accompanied by resources, guidance, and enforcement mechanisms that make quantum security a compliance issue rather than a nice-to-have technology initiative. Companies that have delayed action are now scrambling, while those that started early have a competitive advantage in understanding what migration actually entails.
Post-Quantum Cryptography Standards Are Now Finalized
The technical path forward was clarified when NIST finalized its Post-Quantum Cryptography (PQC) standards in August 2024, providing organizations with approved algorithms that quantum computers cannot easily break. This wasn’t a theoretical exercise—NIST tested, evaluated, and selected algorithms based on real-world cryptanalysis and performance considerations. The standards include multiple options for different use cases, and the process continued into 2025 when NIST selected an additional algorithm, HQC, expanding the toolkit for quantum-safe implementations. The finalization of these standards has triggered real-world adoption among major technology companies. Google has set a 2029 internal deadline for migrating its infrastructure to post-quantum cryptography, recognizing that this represents a multi-year engineering effort.
Apple integrated post-quantum encryption into iMessage, making it available to hundreds of millions of users. Cloudflare reports that by late 2025, the majority of human-generated traffic crossing its network was protected by post-quantum encryption. These aren’t pilot projects—they’re production deployments protecting real users and real data. The limitation of all this progress, however, is that most organizations haven’t started. While tech giants are well into implementation, many mid-market and smaller companies are still in the assessment phase.
Building a Migration Strategy Within the Time Constraint
Most organizations planning post-quantum migration should expect the process to take between 2 and 5 years depending on the complexity of their systems, the number of legacy applications involved, and their starting point. This timeline isn’t arbitrary—it reflects the reality that cryptography is woven throughout modern infrastructure. Keys need to be generated and distributed, algorithms need to be integrated into applications, infrastructure needs to be updated, and everything needs to be tested to ensure no encrypted data breaks or becomes inaccessible. A startup or relatively modern application might move toward the shorter end of this range; a financial institution or government contractor with decades-old systems embedded throughout their operations might find themselves at the five-year mark.
The tradeoff between speed and thoroughness is real and unavoidable. Companies that rush the migration risk implementing post-quantum cryptography incorrectly, potentially creating new vulnerabilities while attempting to patch the old ones. Conversely, companies that move too slowly risk violating compliance deadlines and potentially facing contract terminations or regulatory action. The practical solution most organizations are adopting involves a hybrid approach: immediately beginning work on new systems and external-facing services using post-quantum algorithms while running parallel encryption environments (classical and quantum-safe) on critical systems. This approach is slower to fully implement but reduces the risk of breaking production systems during the transition.
Market Dynamics Show the Scale of the Shift
The financial commitment required for quantum-safe migration is enormous, which explains why global cybersecurity spending is projected to reach $240 billion in 2026, an increase of 12.5% year-over-year. While not all of this is quantum-related, a significant and growing portion reflects the cost of assessment, planning, and implementation of post-quantum solutions. Gartner’s forecast implicitly recognizes that quantum security isn’t just another security category—it’s becoming a central pillar of how companies allocate security resources. The market opportunity is attracting significant investment.
The post-quantum cryptography market, currently in its growth phase, is expected to expand at a compound annual growth rate of 37.1% from 2025 through 2034, reaching a market size of approximately $6.98 billion by 2034. This explosive growth reflects both the technical complexity of the migration (requiring specialized expertise and tools) and the broad scope of the challenge (affecting nearly every organization that handles digital information). However, this market growth also comes with a warning: the rapid emergence of new vendors and solutions creates a selection problem for companies. Not all post-quantum solutions are equal, and choosing poorly could mean costly rework when standards evolve or vulnerabilities emerge in less-vetted approaches.

Real-World Implementation Examples
Concrete examples of quantum-safe deployment are beginning to emerge outside the major tech companies. IonQ, a quantum computing company, is partnering with Florida LambdaRail to deploy a quantum-safe communication network across Florida using Quantum Key Distribution (QKD) technology. This deployment serves as a proof-of-concept for how quantum security infrastructure can be implemented in specific geographic or organizational contexts.
These initiatives demonstrate that quantum-safe security isn’t relegated to theoretical discussions or lab environments—it’s becoming operational reality. EvolutionQ, a private company founded in 2015, focuses specifically on quantum-safe security solutions for critical infrastructure protection. The existence and growth of specialized companies like EvolutionQ shows how quantum security is becoming a distinct category within the broader security industry, with dedicated expertise and purpose-built solutions. These companies are not generic cybersecurity vendors rebranding old products—they’re building new infrastructure specifically designed to address the post-quantum threat landscape.
The Timeline Ahead
The path forward is shaped by several key dates and milestones. The NSA’s January 2027 deadline for national security systems is approaching quickly—less than a year away as of 2026. Meanwhile, Google’s 2029 internal deadline suggests that even with substantial resources and engineering expertise, a complete infrastructure migration takes three to four years of sustained effort. Looking further ahead, most expert consensus points to 2035 as a rough estimate for when a cryptographically relevant quantum computer could emerge and threaten current encryption standards.
This creates an implicit deadline: organizations need to be substantially migrated to post-quantum cryptography before that date, which means beginning or accelerating migration efforts immediately if not already underway. The quantum computing arms race is also shaping security priorities. While cryptographically breaking encryption is one risk vector, the existence of quantum computers will unlock new capabilities in optimization, simulation, and machine learning that could have both beneficial and harmful applications. Companies that begin their quantum-safe migration now aren’t just protecting against encryption threats—they’re establishing familiarity with quantum technologies and building organizational capacity to adapt as quantum computing itself becomes more prevalent.
Conclusion
Companies are preparing for quantum computing risks through a combination of regulatory compliance, technical infrastructure overhaul, and strategic investment. The convergence of NSA mandates, finalized NIST standards, and accelerating timelines for quantum computers has transformed quantum security from a future concern into an immediate priority. Major technology companies have already begun implementation, government agencies are requiring compliance, and the market is responding with new solutions and significant capital investment.
The shift represents one of the largest cryptographic transitions in modern computing history. Organizations that act now—whether small startups or large enterprises—have the advantage of learning from early adopters and implementing solutions while expertise is abundant and standards are clear. Those that delay will face compressed timelines, higher costs, and potentially compromised systems. The question for most companies is no longer whether to implement post-quantum cryptography, but how quickly they can execute a migration that protects their data, meets regulatory requirements, and positions them for whatever comes next in the quantum era.