Modern browsers and development environments increasingly implement safety features that require an extra step before allowing pasted commands to execute in terminals and consoles. Instead of instantly running code or commands you paste, many tools now require you to press Enter or confirm the action separately—a small but deliberate friction point designed to prevent accidental execution of malicious code. This security mechanism has become standard across Chrome DevTools, Firefox Developer Tools, terminal applications, and many integrated development environments, emerging from real incidents where users unknowingly pasted and executed harmful commands copied from untrusted sources.
The feature addresses a surprisingly common vulnerability vector. A developer might copy what appears to be a legitimate npm install command from a tutorial or Stack Overflow post, only to find it contains hidden characters or actually executes something entirely different. Because pasting directly into a terminal or console would run the command immediately without visual verification, attackers exploited this by embedding malicious commands in code snippets or misleading documentation. The safety feature forces a moment of confirmation—pasting alone doesn’t trigger execution, preventing these drive-by attacks.
Table of Contents
- Why Do Developer Tools Block Direct Command Pasting?
- How This Safety Feature Works Across Different Tools
- How This Impacts Developer Workflow
- Practical Workarounds and Alternative Approaches
- Common Frustrations and Limitations of This Approach
- Best Practices When Pasting Code and Commands
- The Future of Command Execution Security
- Conclusion
Why Do Developer Tools Block Direct Command Pasting?
The root cause of this security feature lies in a specific type of attack called “paste jacking” or command injection through clipboard manipulation. When you copy text from a webpage, it might contain invisible characters, Unicode tricks, or shell metacharacters that fundamentally change what executes. For example, a paste that appears to be `npm install lodash` might actually contain a hidden newline and additional commands like `rm -rf /` or a curl request sending your credentials to an attacker’s server. The human eye can’t easily spot these manipulations, especially when syntax highlighting is unavailable in a terminal prompt.
Real incidents demonstrate the risk. In 2017, researchers discovered that attackers were posting seemingly helpful code snippets on forums with embedded commands that would steal SSH keys or cryptocurrency wallets. Developers, trusting the source or simply in a hurry, pasted these snippets into their terminals and compromised their systems. Security researchers also found malicious npm packages with names similar to legitimate ones, distributed through pasting shortcuts. These incidents created momentum for browser vendors and terminal developers to implement paste confirmation requirements.
How This Safety Feature Works Across Different Tools
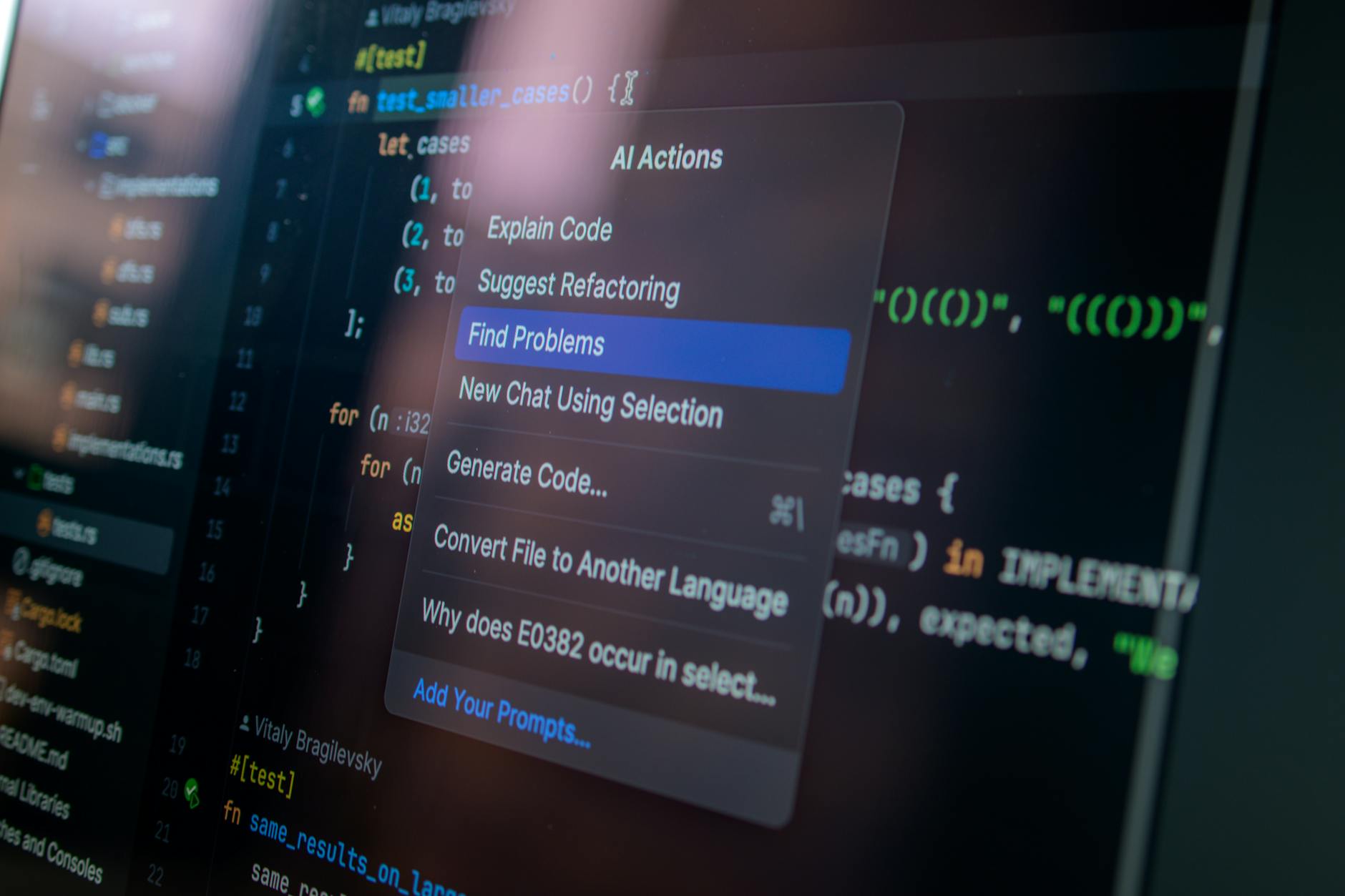
In Google Chrome’s DevTools, pasting certain commands into the console requires typing a confirmation message first—you must literally type `allow pasting` before any pasted code executes. This isn’t a casual inconvenience; Chrome’s implementation prevents pasting JavaScript code that could exfiltrate data, modify the page, or perform actions on behalf of the logged-in user. Firefox implemented a similar but slightly different approach, warning users when pasting multi-line code and requiring explicit confirmation. The limitation here is that this protection doesn’t distinguish between legitimate and malicious code.
A developer pasting a harmless helper function faces the same friction as someone pasting code from an untrusted source. Terminal applications like macOS’s Terminal and many Linux shells prevent pasting raw commands unless they’re already complete (ending with a newline). iTerm2, a popular macOS terminal, requires users to explicitly allow “paste slowly” or goes through a warning dialog for pasted content. The tradeoff is significant: security improves measurably, but legitimate workflows requiring bulk command pasting become noticeably slower.
How This Impacts Developer Workflow
For developers managing infrastructure or running scripts, this feature introduces tangible friction. Consider a DevOps engineer deploying a complex multi-command sequence: without paste confirmation, they’d paste a shell script containing 10+ commands and execute them in seconds. With the safety feature, they now need to either type each command individually, use alternative approaches like downloading the script file and executing it, or navigate through confirmation dialogs. For startups operating under tight deadlines, these accumulated delays compound across a team.
The impact varies by tool and workflow. Developers using Browser DevTools occasionally are barely inconvenienced—typing the confirmation message takes five seconds. But engineers working in terminals for eight hours daily, regularly pasting commands for deployments, database operations, or log analysis, experience genuine productivity drag. A concrete example: deploying via bash scripts that install dependencies and restart services might require multiple paste-and-confirm cycles instead of running as a single batch. Some teams have adapted by using alternative methods like SSH, configuration files, or deployment systems that don’t trigger these restrictions.
Practical Workarounds and Alternative Approaches
The most straightforward workaround is downloading and executing script files rather than pasting their contents. Instead of copying a deployment script and pasting it into the terminal, you can curl the file directly: `curl https://example.com/deploy.sh | bash`. While this approach avoids the paste restriction, it introduces its own security consideration—executing code directly from the network. More controlled environments use configuration management tools like Ansible, Terraform, or Docker, which let you version control and review commands before execution rather than relying on clipboard operations.
For developers who legitimately need to paste commands frequently, several alternatives exist. Using SSH sessions with automatic command execution, leveraging deployment platforms that handle command execution server-side, or using IDE features like pre-configured run configurations can bypass the paste restriction entirely. Firefox’s browser extension ecosystem includes tools that automate certain actions without requiring manual pasting. The comparison is important here: yes, the safety feature slows things down, but the alternatives (version control, automated deployment, infrastructure-as-code) are often more reliable and auditable than manual pasting anyway.
Common Frustrations and Limitations of This Approach
Despite good intentions, the paste confirmation feature has created genuine pain points and workarounds that sometimes undermine the original security goal. Some developers, frustrated with the repeated confirmation prompts, have started pasting code into text editors first, then copying from the editor to the terminal, essentially circumventing the safety check with an extra step. Others modify their terminal settings or use older tools with fewer restrictions, potentially exposing themselves to the very risks the safety feature was designed to prevent. A critical limitation: this feature provides false confidence without preventing all attack vectors.
A determined attacker can still exploit other methods, like social engineering, misleading documentation, or compromised dependencies listed in package managers. The paste blocking primarily prevents accidental or thoughtless execution of harmful code, not sophisticated supply chain attacks. Furthermore, power users and automation tools often have ways around these restrictions—some environments allow configuration changes to disable the confirmation, and scripting languages can read clipboard content programmatically. The protection is meaningful for casual users but incomplete against sophisticated threats.

Best Practices When Pasting Code and Commands
The safest approach to any pasted code is treating it with suspicion, even when the source appears trustworthy. Before pasting any command, read it carefully—understanding what it does before executing. If you must paste complex commands, paste them into a text editor or IDE first where you can read and modify the code before execution.
For code from the internet, trace its origin: is it from official documentation, a verified source, or an anonymous forum post? Commands from official vendor documentation are generally safer than similar-looking code from random websites. For teams and startups, establishing code review practices for scripts and deployment commands reduces reliance on the paste confirmation feature as your only safeguard. Infrastructure-as-code approaches, version control for all scripts, and peer review before deployment prevent many attack vectors entirely. Modern container systems and deployment platforms handle much of what developers previously pasted manually, shifting the security responsibility to platform maintainers rather than individual developers making moment-to-moment decisions about what to execute.
The Future of Command Execution Security
As security threats evolve, expect further refinements to how development tools handle pasted commands and executed code. Some research suggests more sophisticated clipboard monitoring that could distinguish between intentional pastes and automated clipboard access, or tools that analyze pasted code for obviously malicious patterns. The tension between security and usability remains unresolved—future tools may implement adaptive protections that vary restrictions based on context, source, or user behavior.
Longer term, the industry continues moving toward execution environments where pasting commands becomes unnecessary. Containerization, cloud-native development, and infrastructure-as-code mean that fewer developers need to manually paste and execute commands in production environments. For those who do, the expectation increasingly favors using formal deployment pipelines rather than direct command execution. This evolution makes the paste-blocking feature less frustrating not because it disappears, but because the workflows it affects become less central to daily development.
Conclusion
The system safety feature that blocks quick command pasting addresses a real security vulnerability, preventing casual users from accidentally executing malicious code embedded in copied commands. While the friction this introduces is noticeable, it represents a reasonable tradeoff between security and usability—the confirmation requirement has likely prevented countless incidents of compromised systems and stolen credentials.
For startups and development teams, the practical response is implementing proper deployment infrastructure, code review processes, and configuration management tools that reduce reliance on manual pasting. Rather than viewing the paste confirmation as an obstacle, teams should use it as a reminder that direct command execution is an increasingly outdated practice. The future belongs to version-controlled, reviewed, and automated deployment rather than to copy-paste workflows anyway.